cross-posted from: https://lemmy.world/post/12199398
TLDR version as per Signal’s Mastodon:
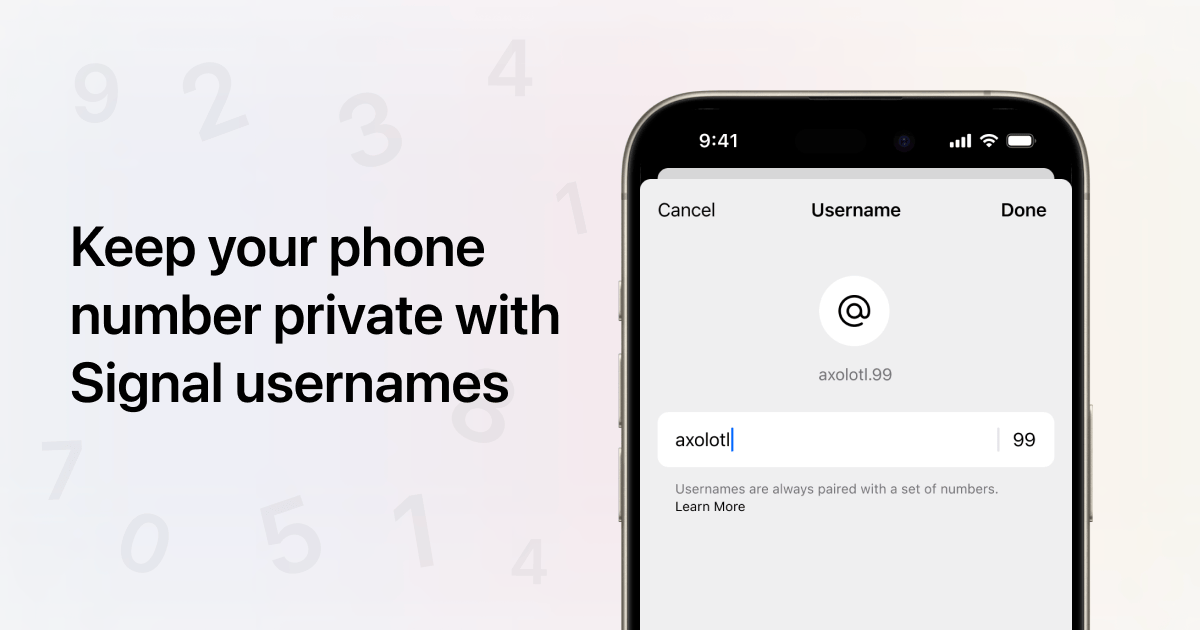
Introducing usernames and phone number privacy on Signal!
We’re making it possible for people to connect with each other without having to share phone numbers. Now launching to beta users, available for everyone soon.
- New default: Your phone number will no longer be visible in Signal
- You can create an optional username to connect without sharing your phone number
- You can enable a new, optional privacy setting to require people to connect with you via username instead of phone number
A Signal username isn’t the profile name that’s displayed in chats, and isn’t visible to the people you chat with on Signal. A username is simply a way to initiate contact on Signal without having to share your phone number. (You still need a phone number to sign up for Signal.)
Create a username by going to your Settings > Profile. Your username must be unique, and can be changed at any time.
To connect with someone via username instead of phone number, type their exact, unique username.
We’re launching these updates to our beta users now, and will be turning them on for everyone running the latest version of the Signal app soon. Our goal is to listen to your feedback, make adjustments, and ensure phone number privacy on Signal is easy and useful for everyone.
You can sign up for beta to test these features. Note that Apple caps the number of iOS beta testers, and we have reached that limit. If you use Signal on iOS, you can get around this by signing up for Desktop beta, linked to your iOS account. See more: https://support.signal.org/hc/en-us/articles/360007318471-Signal-Beta
For more information: Signal’s Blog Post


Is it worth noting that the single key that allows you to sign into a new device basically downloads a list of all the per-message keys, something that can also be experienced if you manually export it on one device and import it on another, even allowing you to see the JSON they use to store it?
For what it’s worth, in my 2018 era experience with the software, it was really easy to sign on to a new device without this key, but I couldn’t access old messages (they would appear, in bulk, but they would all say “unable to decrypt”)
Yes, that is exactly where perfect forward secrecy fails in Element. It allows all of the message keys to be downloaded by attacking a single point of failure. Perfect forward secrecy would necessitate that all messages and their encryption keys be completely independent, and each message would need to be broken one-by-one, as each key is completely different. What Element does with their cloud backup solution is it adds a single point of failure that results in every single message being compromised, without physical access to any device. Real perfect forward secrecy would make that impossible, as you have to break the encryption of every message independently (again, ignoring physical access to the device, because the device will always have access to all the messages anyway). It essentially invalidates many of the benefits of using a double-rachet key exchange protocol to begin with, as you can attack a single point of failure that would compromise all messages instead.
Granted, whether or not that matters to you is entirely up to you. I’m just clarifying that Element lacks perfect forward secrecy, so I have an ideological objection to my own personal use of it for anything sensitive, since there are more secure messengers out there (like SimpleX) that do have perfect forward secrecy, and many more security and privacy features (like the whole no user identifiers thing and no server side storage with SimpleX). That does of course come with the tradeoff that you can only use it on one device at a time, but everything is a list of pros and cons. Is anyone going to target you and attack you by attempting to gain access to your cloud backup keys? No, most certainly not. But the fact that it exists as an attack vector to begin with is troubling from a security perspective (again, that’s where SimpleX shines with all data being stored locally, so there is no way to access those messages on demand without physical access to the device). I personally think that the metadata issues are much worse with Matrix from an immediate privacy perspective, as that is an avenue that can be actively exploited in a much easier capacity.
If I understand correctly though, I believe we’re both on the same page. Element is still a much better option than something like Discord, but it is not without its own flaws.