- cross-posted to:
- selfhosted@lemmy.world
- technology@beehaw.org
- cross-posted to:
- selfhosted@lemmy.world
- technology@beehaw.org
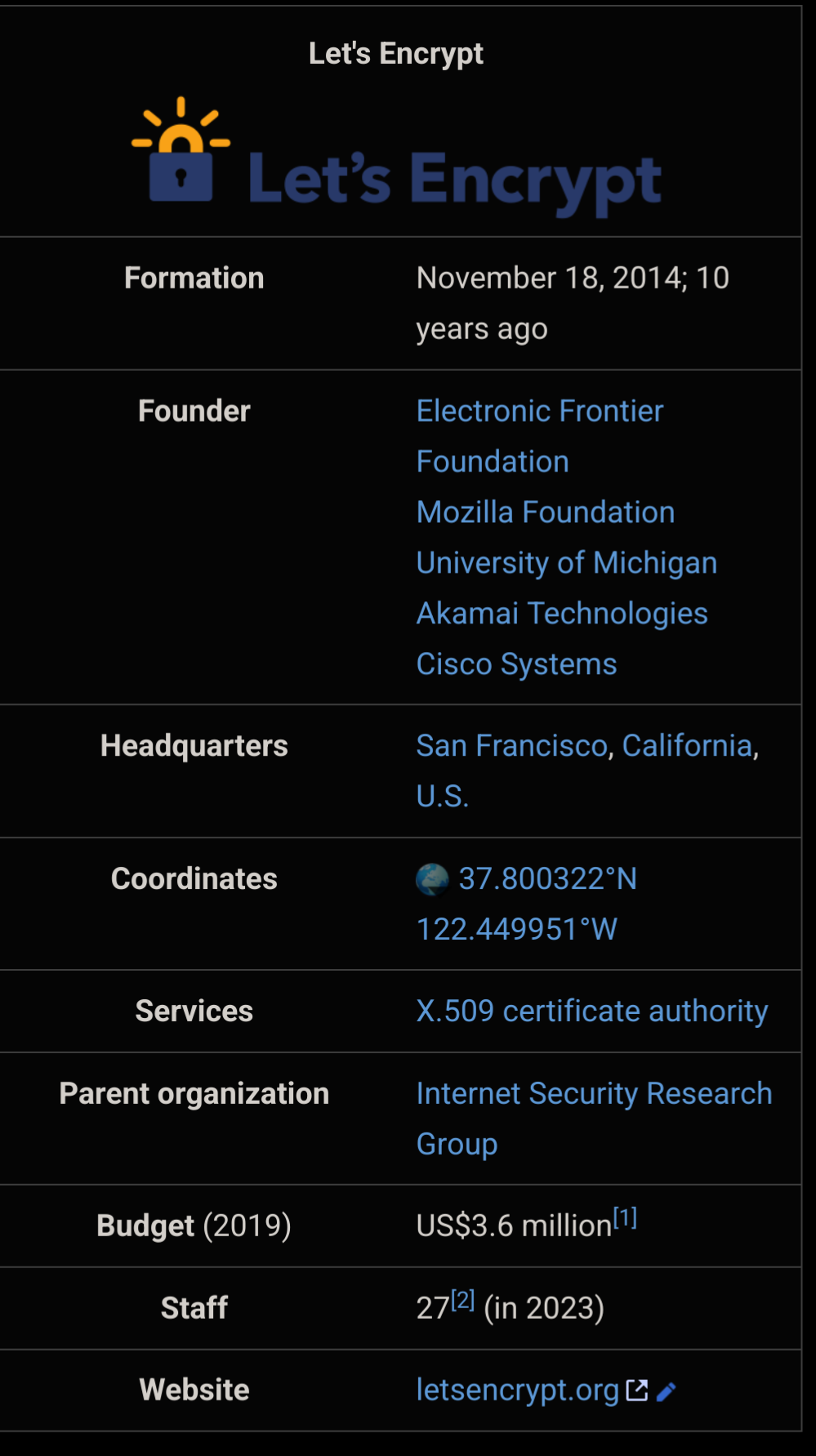
Happy birthday to Let’s Encrypt !
Huge thanks to everyone involved in making HTTPS available to everyone for free !
A client of mine pays for an SSL cert he doesn’t even use. I’ve told him before I moved him to Let’s Encrypt because I was able to automate the renew process. He decided he needed to continue paying for the SSL cert. I told him we are not using it, but he doesn’t believe me. So he continues to pay for it.
I love it when companies are too stubborn to update their costs despite the necessity changing over the years.
My previous employment kept buying microsoft office license keys despite us already moving to 365. They probably did it out of habit when buying new computers. Needless to say I have a cardstack of license keys at home lol. Granted it’s for Office 2013 but I don’t really need the latest version for basic document processing.
Private sector is more efficient my ass
TLS certificates have huge margins, so web hosts love selling them.
And it changed the Internet, for good and a lot.
I worked for a company we had 300 websites, the boss wanted to buy certs. I told him about Lets Encrypt. He loved the idea it saved us a bunch of money. I suggest we donate $100 to them. Hes says “NO F-ing way!”.
That’s very great news! Thank you for all the good work!
Just two months ago, a security team member dinged one of our services for using Lets Encrypt, as “it’s not as secure as a traditional CA”.
It’s sad that these arguments are still being shared. It was the same arguments years ago from people that would just assume that a free cert was inherently unsafe.
I’d love for them to explain how, if anything the short cert validity and constant re-checking of the domain seems more secure than traditional CAs
I’d also argue that the fact that it’s 100% automated and their software is open source makes it objectively more secure. On the issuing side, there’s no room for human error, social engineering, etc.
Underrated. Stuff rocks.
SSL Certs were so god awful before certbot that it’s hard to explain now that it’s so easy and free.
Also fucking expensive
Lol I instinctively freaked out when I saw the post preview assuming it was going to be a post about a major data breach or exploit of some sort relating to Let’s Encrypt.
I probably need more positivity in my life 😂
Sleeping too well lately? Consider this:
If LetsEncrypt were to suffer a few weeks outage, how much of the internet would break?
If you have a fully automated setup. Youll have 30 days to mitigate the fallout.
It won’t be that simple.
For starters, you’re assuming t-zero response. It’ll likely be a week before people worry enough that LE isn’t returning before they act. Then they have to find someone else for, possibly, the hundreds or thousands of certs they are responsible for. Set up processes with them. Hope that this new provide is able to cope with the massive, MASSIVE surge in demand without falling over themselves.
And that’s assuming your company knows all its certs. That they haven’t changed staff and lost knowledge, or outsourced IT (in which case they provider is likely staggering under the weight of all their clients demanding instant attention) and all that goes with that. Automation is actually bad in this situation because people tend to forget how stuff was done until it breaks. It’s very likely that many certs will simply expire because they were forgotten about and the first thing some companies knows is when customers start complaining.
LetsEncrypt is genuinely brilliant, but we’ve all added a massive single point of failure into our systems by adopting it.
(Yeah, I’ve written a few disaster plans in my time. Why do you ask?)
Piggybacking off this comment because I completely agree with it.
Did we not learn anything from CrowdStrike? If a comparatively simple fix was able to wipe out half the world, how would something that requires an active choice (where to get certs from) not completely cripple all of our infrastructure?
And my parents still buy SSL certs because that’s just what they know 🤢
Today it’s just more or less stupid to buy SSL you can get one extremely easy for free from Let’s Encrypt or Google Trust…
Yeah, I uh…I think that’s kinda what this whole conversation here is about
I’ve tried explaining to them before, but they think that it’s a scam because it’s free lol
My last cert renewal was $20 for 3 years. That’s less than a dollar a month, not exactly breaking the bank.
Can anyone fill me on this? Why is it so significant?
HTTPS certs used to be very expensive and technically complicated, making it out of reach for most smaller orgs. Let’s Encrypt brought easy mass adoption and changed encryption availability on the web for everyone.
They also made it a open protocol (the ACME protocol), so now there’s a bunch of certificate providers that implement the same protocol and thus can work with the same client apps (Certbot, acme.sh, etc). I know Sectigo and GoDaddy support ACME at least. So even if you don’t use Let’s Encrypt, you can still benefit from their work.
deleted by creator
And it shouldn’t have been, SSL PKI is an intentionally rigged architecture. It’s intended for nation-states to be able to abuse it.
I’d like much more some kind of overlay encryption over HTTP based on web of trust and what not. Like those distributed imageboards people were trying to make with steganography in emotion.
It’s a trap. Everybody is already in it and it has already been activated, so - the discussion would be of historical interest only.
Lots of people shitting on stories of people who buy certs.
You do still have to buy a cert if you want one for a .onion. Let’s encrypt still doesn’t support it :(
But…an onion address doesn’t need a cert?
Some apps refuse to work if you dont have TLS, so it depends what you’re running
I’m also having to manually cert every 3 months for my emby instance. It’s a minor inconvenience, but I’m definitely tempted to just buy a yearly.
Emby?
Same idea as Jellyfin / Plex. Self hosted media server. Plex handles ssl certs for you, Emby doesn’t have an automatic process so I’m having to manually replace it every 90 days
Why not use a reverse proxy with this built in? Caddy, Traeffik…
Why not script it so you don’t have to do it manually?
Your advice is sound, my ability to focus on such a task however… lol
I’m sad to say that all my sites where http only until 10 years ago
It doesn’t say on the website but on their anniversary day they are giving away unlimited ssl certs!
Well, they do rate limit
Huge impact on a tiny budget - that’s extremely impressive. The world could be so much better without rent seeking parasites.








