This is the best summary I could come up with:
Researchers on Wednesday presented intriguing new findings surrounding an attack that over four years backdoored dozens if not thousands of iPhones, many of which belonged to employees of Moscow-based security firm Kaspersky.
Chief among the discoveries: the unknown attackers were able to achieve an unprecedented level of access by exploiting a vulnerability in an undocumented hardware feature that few if anyone outside of Apple and chip suppliers such as ARM Holdings knew of.
“The exploit’s sophistication and the feature’s obscurity suggest the attackers had advanced technical capabilities,” Kaspersky researcher Boris Larin wrote in an email.
“Our analysis hasn’t revealed how they became aware of this feature, but we’re exploring all possibilities, including accidental disclosure in past firmware or source code releases.
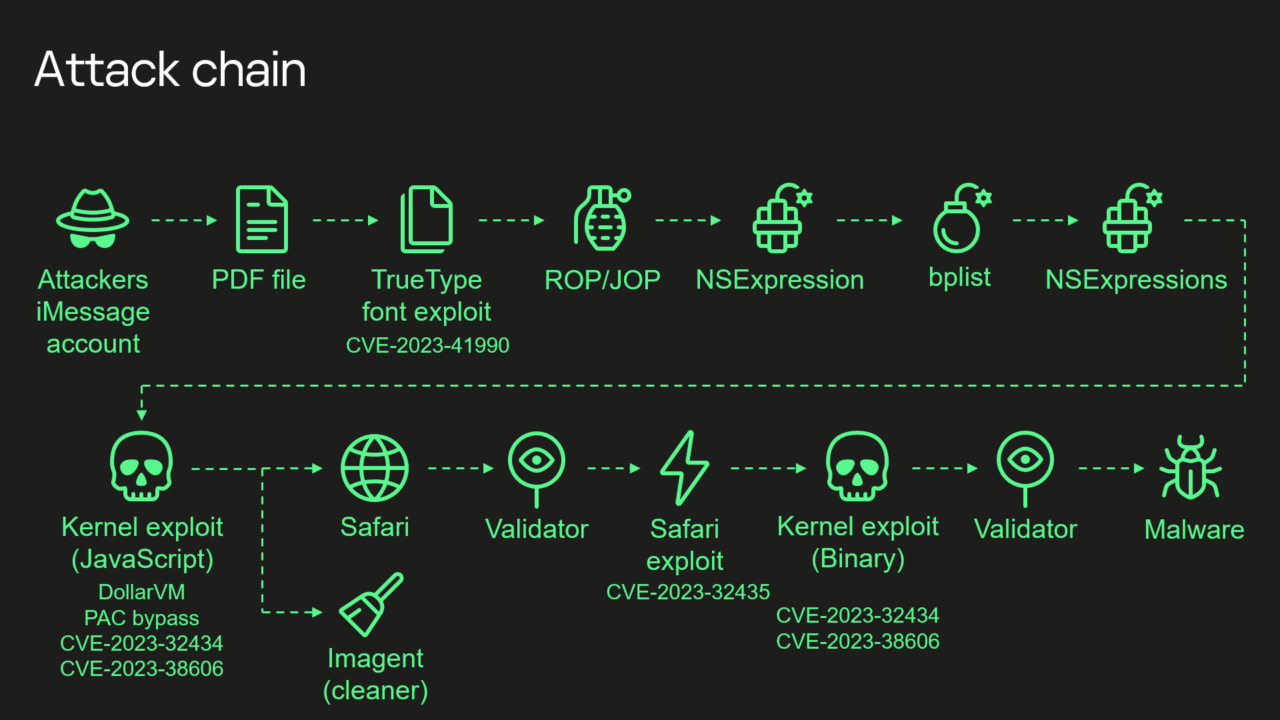
A fresh infusion of details disclosed Wednesday said that “Triangulation”—the name Kaspersky gave to both the malware and the campaign that installed it—exploited four critical zero-day vulnerabilities, meaning serious programming flaws that were known to the attackers before they were known to Apple.
The researchers found that several of MMIO addresses the attackers used to bypass the memory protections weren’t identified in any device tree documentation, which acts as a reference for engineers creating hardware or software for iPhones.
The original article contains 653 words, the summary contains 200 words. Saved 69%. I’m a bot and I’m open source!
The exploit’s sophistication and the feature’s obscurity suggest the attackers had advanced technical capabilities
exploiting a vulnerability in an undocumented hardware feature that few if anyone outside of Apple and chip suppliers such as ARM Holdings knew of.
according to Russian officials also infected the iPhones of thousands of people working inside diplomatic missions and embassies in Russia
the devices were infected with full-featured spyware that, among other things, transmitted microphone recordings, photos, geolocation, and other sensitive data to attacker-controlled servers
Sounds like government espionage
puts tinfoil hat on
It’s not purely talent that allows them to make this kind of stuff. Otherwise people outside of these agencies would be making this stuff too. It’s also the fact the CIA or any of the others can go to apple for example and get all of the information on how these chips are made and the firmware on them, then put the company under a gag order.
It is silly to assume the governments hackers are any better then a good hacker that doesn’t work for them. And you need to realise that their advantages come from legal power, resources, and lesser regulations on research.
Because a lot of silly conspiracy theories seem to stem from people believing that the government are somehow superior beings, when the only thing that makes them different from anyone else is power.
Can’t wait to listen to the Darknet Diaries interview about this in a few years.
How do you find those podcasts, sometimes the stories are really interesting but I think he is running thin on ideas.
not op, but I think it depends a lot on the person he’s interviewing
It’s important to reboot your devices frequently
I recently invented a “People First” Cybersecurity Vulnerability Scoring method and I called it CITE, Civilian Internet Threat Evaluation with many benefits over CVSS. In it, I prioritize “exploit chains” as the primary threat going forward. Low and behold, this new exploit, although iOS, possibly one of the most sophisticated attacks ever using one of the longest exploit chains ever! Proof positive!
Depending on how you define it; I define the Kaspersky diagram has 8 steps. In my system, I define steps that advance the exploit discretely as stages, so I would evaluated Triangulation to be a 4 stage exploit chain. I should tally this attack to see how it scores and make a CITE-REP(ort).
You can read about it if interested. An intersting modeling problem for me was does stages always equate to complexity? Number of exploits in the chain make it easier or harder to intrusion detect given that it was designed as a chain, maybe to prevent just that? How are stages, complexity, chains and remediation evaluted inversely?
Thanks for sharing! I’m amazed at how sophisticated this was.
Wow, this is a very complex exploit, involving bits of iMessage and an undocumented CPU feature that allowed the attacker to evade hardware memory protection. From what I can see, Lockdown mode would have prevented this. The attacker is ridiculously skilled regardless
Exerpts from the article missing from the bot summary:
The mass backdooring campaign, which according to Russian officials also infected the iPhones of thousands of people working inside diplomatic missions and embassies in Russia, according to Russian government officials, came to light in June. Over a span of at least four years, Kaspersky said, the infections were delivered in iMessage texts that installed malware through a complex exploit chain without requiring the receiver to take any action.
With that, the devices were infected with full-featured spyware that, among other things, transmitted microphone recordings, photos, geolocation, and other sensitive data to attacker-controlled servers. Although infections didn’t survive a reboot, the unknown attackers kept their campaign alive simply by sending devices a new malicious iMessage text shortly after devices were restarted.
The most intriguing new detail is the targeting of the […] hardware feature […]. A zero-day in the feature allowed the attackers to bypass advanced hardware-based memory protections designed to safeguard device system integrity even after an attacker gained the ability to tamper with memory of the underlying kernel.
someone was made fun of one too many times about having green bubbles in imessage
With that many exploits being used I wouldn’t be surprised to see it is a group probably government sponsored. They love iMessage exploits as original attack vectors too.
Can the US government pass a law to force Apple specifically to rip out the messages app and replace it with something that apparently doesn’t have infinite exploits??
Does ios have any ROP mitigations?